What is a 5G private network?
In recent years, 5G private networks have emerged as an indispensable and popular solution for enterprise and government clients’ industry networking needs. It seems that 5G has become an omnipotent network capable of solving all scenarios and connectivity requirements. But is this really the case?
Certain telecom operators are promoting 5G private networks as a key focus in their enterprise and government projects, but for these operators themselves, are these networks a pot of honey or a bottle of poison?
How many technical types of 5G private networks exist? What are their respective characteristics, advantages, and applicable scenarios?
This article aims to answer these pressing questions of general interest.
Before delving into 5G, it is essential to understand: What is 5G? For an overview of the technological evolution and background from 1G to 5G, you can refer to the article “5G is Coming: A Comprehensive Guide to Its Past, Present, and Future”. Although this was written in 2018, before large-scale 5G deployment, its fundamental principles remain relevant today.
I. 4G/5G Public Wireless Network Technology – Public Network for Public Use
4G and 5G technologies are operator-led, so-called “public network technologies” (available to all members of the public, not targeting specific groups or users). Typically, devices connect to the Internet through the public networks operated by telecom carriers (China Telecom, China Mobile, China Unicom, and China Broadcasting Network). While 4G/5G wireless technologies can meet the needs of small-data-volume, non-real-time information transmission, they are highly unsuitable for IT intelligent networking. This is particularly true for high-capacity HD video scenarios or intelligent control scenarios involving remote operations, manifesting in several limitations:
- Access Limitations:
- Data transmission relies on the operator’s mobile communication infrastructure, which is constrained by base station deployment. Outside urban areas, 5G communication quality and reliability cannot be guaranteed. However, these areas are precisely where many IT intelligent projects are most critical (e.g., water conservancy, ports, oil & gas). A dedicated network offering high reliability, large capacity, and high bandwidth is therefore imperative.
- 4G and 5G are designed primarily for network access by smartphones and similar intelligent terminals. Consequently, parameters like latency, speed, and capacity are optimized for such devices. The actual carrying capacity of deployed base stations is generally correlated with the user density in the coverage area. If a large volume of video traffic (uplink) floods in and persists, it will severely deplete system resources and may even cause base station equipment to crash. In other words, relying on 4G/5G for intelligent networking and HD video transmission may simply be technically unfeasible.
- Bandwidth Limitations:
- HD video surveillance is now a standard component in many IT intelligent systems, requiring real-time transmission of large-capacity IP HD images over the network. When a large number of video streams are concurrent within a small area, telecom operators’ 4G/5G base stations cannot meet the demands in terms of either bandwidth (limited by frequency resources, etc.) or reliability. Instead, a true broadband IP network access system with dedicated network resources is essential.
- Currently, the effective data rates of 4G/5G networks are relatively low, fully unable to meet the bandwidth requirements of HD video surveillance (a typical 1080P stream requires 4Mbps). Moreover, 5G coverage in rural areas may not be realized for many years. Additionally, across all 4G/5G standards, uplink speeds are lower than downlink speeds, making them highly unsuitable for video surveillance applications that generate significant upload traffic.
- Prohibitive Costs:
- Many intelligent systems generate substantial traffic, especially for HD video surveillance. A single 1080P HD video camera can consume 1000-2000GB of data per month. Even at the current most favorable IoT data plan rate of 1 RMB per GB, this would cost 2000 RMB per month per camera. With multiple cameras running 24/7, the costs become astronomical, even for financially robust enterprise and government users.
- There are also associated environmental costs. After large-capacity video is transmitted to the Internet, it needs to be routed back to the monitoring center. This typically requires the operator to lease a large-capacity dedicated Internet line with a fixed IP address, costing tens of thousands to hundreds of thousands of RMB annually. Alternatively, using a third-party “cloud platform” for video transit incurs additional expenses for cloud platform rental and dedicated VPN lines, which are similarly costly. As a result, most users find these costs prohibitive.
- Security Concerns:
- Accessing via 4G/5G typically requires relaying through an Internet cloud platform or having an Internet-routable IP address. Using the public Internet in this way exposes the system to the risk of global hacking attacks. Ensuring security would necessitate a professional security team, which is impractical for most users.
- For control scenarios requiring high security, such as water conservancy sluice gates, port cranes, and numerous IT intelligent systems requiring a security level of Grade 2 or higher, using a public network poses significant risks. Physical isolation is a must. For more on the importance of physical isolation in such system networking, refer to the article “The 5G Era: Network Security and Physically Isolated Private Networks in Enterprise and Government Network Construction”.
II. 5G Private Network Methods – Adapting Public Network Technology for Private Use
Precisely because of the various limitations of public networks, 5G private networks have been proposed as an alternative for users. So, what exactly is a 5G private network, and how does it differ?
Currently, there are three main forms of 5G private networks:
- Enterprise/Government Self-built 5G Systems (must be constructed in cooperation with telecom operators, connecting to the operator’s backbone network, and subject to frequency usage fees, management fees, and regulatory control).
- 5G Hybrid Networking (5G Slicing).
- 5G Virtual Private Network (using SD-WAN or VPN technologies).
(I) Self-built Physical 5G Private Network (Standalone Networking)
Since 5G is a public network technology, enterprise and government clients do not have the right to build standalone networks independently. Frequency spectrum is exclusively allocated to telecom operators by the state radio regulatory authority. Therefore, constructing a physically isolated 5G private network must be done in “cooperation” with one of the four major operators. A crucial consideration, which also significantly impacts costs, is whether the core network will be 下沉 (xiàchén – deployed locally/sunk) within the private network. Due to the inherent characteristics of the telecom industry, the cost of self-building a 5G network is extremely high, with a single base station costing hundreds of thousands to millions of RMB. Additionally, ongoing high management fees must be paid to the cooperating operator. From an economic perspective, this is often prohibitive even for wealthy enterprise and government users.
Technically, 5G base stations have a very short coverage radius (typically only 0.5 kilometers). While low-band 5G offers greater coverage, it provides much lower bandwidth and incurs higher standalone deployment costs. To ensure adequate signal overlap and coverage in the target area of an enterprise or government client, numerous base stations are usually required, further escalating investment.
Furthermore, due to limitations in 5G spectrum resources, the achievable bandwidth is constrained, making it unable to meet the demands of applications like IT remote control with large video payloads. More importantly, even with a self-built 5G private network, the end-to-end latency remains relatively high (Note: Unscrupulous vendors often tout the “low latency of 5G base stations” while ignoring a crucial point: wireless latency is only one part of the overall network latency). It is completely unable to satisfy the millisecond-level latency requirements of real-time IT control systems.
Therefore, even though there are some implementation cases of this solution, they are mostly in vehicle networking applications with low bandwidth requirements or low demands on network reliability. Moreover, the effectiveness of many deployed projects is mixed, with several technical issues (such as roaming control) remaining unresolved. This approach is generally unsuitable for large-scale IT intelligent control systems; it may not even be appropriate to use a 5G private network as a hot backup system.
(II) 5G Hybrid Networking (Virtual Private Network)
The other two 5G networking methods fall under the category of virtual private networks. They create a “virtual private network” through algorithms or network technologies, rather than a truly physically isolated one. These two methods are:
1.Virtual Private Networks based on 5G Slicing Technology
Network slicing is a technology that virtualizes multiple end-to-end networks on a common hardware infrastructure. Each network slice possesses distinct network functions tailored to specific service requirements. As illustrated in the 5G network slicing architecture diagram (not shown here), after an operator acquires physical resources, it can create an eMBB (enhanced Mobile Broadband) slice for public Internet access services. It can then create another mMTC (massive Machine Type Communications) slice using the same physical resources to serve smart meter reading needs from certain vertical industry vendors. These two slices provide services for different business scenarios independently.
5G slicing is thus based on network slicing technology. (Diagram of principles not shown here).
1.Virtual Private Networks based on 5G Slicing Technology
Network slicing is a technology that virtualizes multiple end-to-end networks on a common hardware infrastructure. Each network slice possesses distinct network functions tailored to specific service requirements. As illustrated in the 5G network slicing architecture diagram (not shown here), after an operator acquires physical resources, it can create an eMBB (enhanced Mobile Broadband) slice for public Internet access services. It can then create another mMTC (massive Machine Type Communications) slice using the same physical resources to serve smart meter reading needs from certain vertical industry vendors. These two slices provide services for different business scenarios independently.
5G slicing is thus based on network slicing technology. (Diagram of principles not shown here).
The ability of 5G to implement network slicing is inseparable from the support of NFV (Network Functions Virtualization) and SDN (Software Defined Network) technologies.
While vertical industries have diverse demands for network functions, these requirements can all be decomposed into needs for network capabilities such as bandwidth, connection count, latency, and reliability. The 5G standard has also categorized the network function requirements of different services into three typical scenarios, with corresponding network slice types: eMBB (enhanced Mobile Broadband) slices, mMTC (massive Machine Type Communications) slices, and uRLLC (ultra-Reliable Low Latency Communications) slices. Services across different 5G industries can be carried on distinct slice networks. Even different vendors offering the same service can act as tenants of slice networks, purchasing, managing, and operating their own slices to provide communication services to their end customers. A typical application logic is as follows:
Network slicing possesses three key characteristics: “on-demand customization,” “end-to-end,” and “isolation.” It enables the dynamic deployment of end-to-end network services (in terms of location and specifications) based on demand, while ensuring each slice has independent lifecycle management and slices do not interfere with one another.
However, it is crucial to note that network slicing is still built on top of the 5G public network and is inherently constrained by the physical infrastructure of the 5G public network. It can be regarded as an enhancement technology for the 5G public network, but it cannot solve the aforementioned application problems of the 5G public network.
Additionally, 5G slicing is a service customized at the telecom operator level, involving cumbersome coordination. Therefore, projects where this technology is actually implemented are not yet mainstream.
2. Virtual Private Networks (VPN) Based on Virtualization Technologies such as Cloud Exchange (SD-CX)
This approach utilizes public 5G as the underlying network infrastructure. It constructs end-to-end encrypted tunnels through tunneling, authentication, and encryption technologies. Virtual private networks are then established using either VPDN (Virtual Private Dial-up Network) or VPN (Virtual Private Network) technologies.
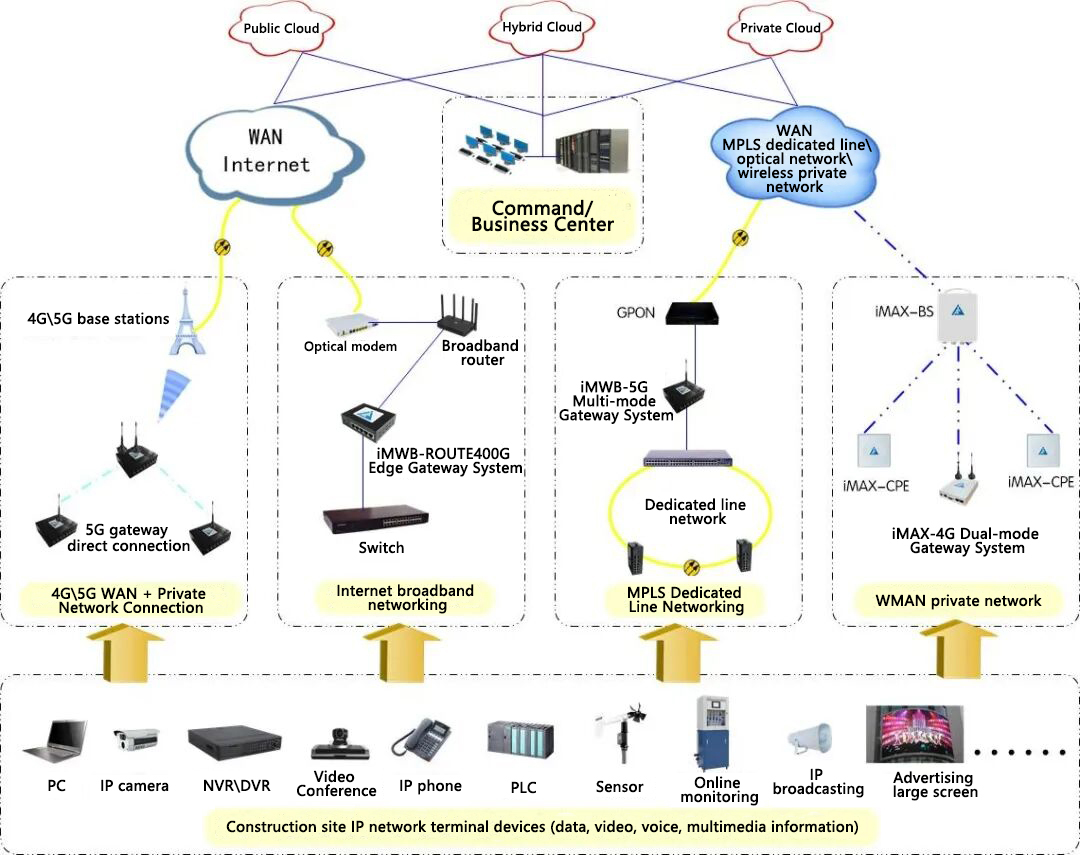
The Guoxin Longxin 5G Virtual Private Network solution is built based on the SD-CX framework and employs VPN technology. A schematic diagram of a typical 5G virtual private network application is shown below:
For details on the Guoxin Longxin 5G Virtual Private Network solution, please refer to the article “5G Virtual Private Networks: Solving Connectivity Challenges for Enterprise and Government Clients”; further discussion will not be provided here.
Whether utilizing 5G slicing or 5G virtualization technologies to form a 5G virtual private network, both approaches fall under the category of hybrid networking. This means they are physically integrated with the operator’s public 5G network but create a “virtual private network” at the logical level or through proprietary network virtualization tunneling technologies.
Hybrid 5G networking not only inherits most of the problems described earlier in the “Wireless Public Network Technology – 4G/5G” section, such as “unreliability, instability, and tidal effects” (characterized by degraded network metrics like packet loss and latency), but also fails to meet the requirements for intelligent control. Additionally, primary transmissions for IT intelligent control, such as high-capacity video, incur astronomical data plan costs. Consequently, these two methods are infeasible for high-capacity video services. They are only suitable for “narrowband IoT” scenarios that do not involve control and have low requirements for reliability and security, or for temporary mobile connectivity needs.
The construction of 5G networks has peaked in terms of end-users and lacks so-called “killer applications” to drive adoption. This has led 5G to compete directly with 4G for customers. As a result, while 5G requires massive investments, the benefits have not increased significantly. Years of investment without a corresponding rise in revenue have burdened operators, and the peak period of 5G construction has passed. Conversely, 5G private network construction is also not operator-friendly. IT and intelligent projects for enterprise and government clients typically involve one-time investments and demand extremely high levels of customization, technology, and service. If 5G private networks fail to live up to the “omnipotent” expectations of users, project execution becomes difficult, and projects may even be abandoned halfway. Therefore, whether 5G private networks are a pot of honey or a bottle of poison for telecom operators truly remains to be seen.
In conclusion, 5G private networks are an excellent technology. Particularly, those based on hardware VPN virtual private network technology can achieve the performance of “dedicated data lines” at a lower cost, meeting the demand for low-cost, remote connectivity among enterprise and government clients while enhancing network security and stability. However, 5G private networks are not a “one-size-fits-all solution” for solving the connectivity needs of enterprise and government clients, nor are they an affordable networking method for ordinary civilian users. For the vast majority of enterprise and government users seeking connectivity in target areas, adopting iMAX 5G Wireless Metropolitan Area Network (WMAN) technology or WiFi-based Wireless Local Area Network (WLAN) technology may be more appropriate.
III. iMAX 5G Wireless Metropolitan Area Network (WMAN) Private Network – A Physical Private Network
iMAX 5G Wireless Metropolitan Area Network (WMAN) technology is a proprietary private network communication technology. Here, “5G” refers to the system operating in the 5GHz wireless frequency band, whereas the “5G” used by telecom operators refers to the “5th Generation Mobile Communication Technology.” These two are fundamentally different. Unfortunately, some industry competitors intentionally conflate this distinction, using the term “5G private network” universally to confuse unsuspecting users. This is either foolish or malicious. Guoxin Longxin would never engage in such practices.
The iMAX wireless communication system is designed to build “wireless cities” and is specifically optimized for transmitting real-time services such as video surveillance. All product series offer exceptional communication distances, with performance and quality that lead the industry. Currently, products like the iMAX-6000 and iMAX-8000 series are widely deployed in enterprise and government private network projects. Key technical features include:
- Communication Distance: Under line-of-sight conditions, iMAX 5G dedicated communication systems can achieve distances exceeding 50 kilometers. Even the smallest integrated antenna systems can easily provide coverage with a radius of 10 kilometers.
- Transmission Bandwidth:
- iMAX-8000H: 300/600 Mbps point-to-multipoint communication system.
- iMAX-8000S: 100 Mbps point-to-multipoint communication system.
- iMAX-6000: 150/300/600 Mbps point-to-point communication system.
- Advanced Technology: The iMAX system supports routing and ring network formation, VRRP (Virtual Router Redundancy Protocol) for high-reliability networking, multi-link data mirroring, and multi-layered network security technologies. It is ideally suited for constructing large-scale, high-capacity fixed and mobile metropolitan area networks.
The iMAX-6000 and iMAX-8000 series are primarily used in building wireless video surveillance systems, with numerous successful cases and applications in domestic industries such as public security, oil & gas, ports, transportation, and forestry. Taking a “disaster early warning private network” as an example, a typical iMAX private network topology diagram is shown below:
Technical Features of Guoxin Longxin’s iMAX5G Broadband Wireless Private Network System:
- Stability & Efficiency: iMAX broadband wireless products offer bandwidths of several hundred megabits per second, fully meeting the real-time connectivity requirements of emergency management systems. They deliver exceptional operational stability and reliability, functioning as true 24/7/365 non-stop operation devices. Furthermore, they provide stable bandwidth and strong anti-interference capabilities.
- Security & Reliability: It is a true private network with a dedicated physical infrastructure. It supports access control, data encryption, VLAN (Virtual Local Area Network) technology, VPN (Virtual Private Network) technology, and firewall technology, ensuring multi-layered and high-standard security for data transmission.
- Cost-Effectiveness: It requires a one-time investment and is more cost-effective compared to leasing. It effectively protects the investment (as devices can be relocated as needed). With easy and quick installation, a short construction period, and simple maintenance, it further enhances overall system cost-efficiency.
- Easy, Fast Installation & Flexible Maintenance: The devices are compact and lightweight. Installation typically takes only 1-2 working days. Maintenance and relocation are also very simple processes.
In addition to the above, leveraging the high-bandwidth characteristics of this wireless access system, it can not only support “three-high services” (high bandwidth, high capacity, high reliability) but also simultaneously carry other services such as IP broadcasting, VoIP (Voice over IP) telephony, police communication terminals, e-government networks, and mobile office. “Converged multi-network” and “mixed multi-service networking” further enhance its comprehensive utilization value.
For enterprise and government clients’ private network construction, especially for high-capacity video and high-reliability network requirements, adopting the iMAX Wireless Metropolitan Area Network (WMAN) system to build a wireless private network is the most suitable, stable, and reliable solution.
IV. Summary
The networking method chosen by government and enterprise clients has a significant impact on the implementation effect of IT and intelligent projects, and may even directly determine the success or failure of the projects. 5G private network is an excellent technology, but it is not the end of the development of the communications industry, nor should it be deified. In the future, there will be the 6th Generation Mobile Communication Technology (6G), the 7th Generation Mobile Communication Technology (7G), and even Next-Generation (NG) technologies. Technological development is endless.
A few words on a digression about 6G: Given the current status of wireless frequency allocation and the scarcity of wireless spectrum, 6G will most likely use millimeter-wave frequency bands in the future, and the coverage radius of a single base station may become shorter. This is an inevitable trend. However, due to the contradiction between the scarcity of wireless frequencies (which leads to limited bandwidth) and the unlimited demand for operators’ public networks, it is difficult to change the data package billing method of telecom operators. It will most likely only result in larger data packages or lower prices per package.
For a specific IT intelligent project of a government or enterprise client, it is necessary to analyze networking needs such as bandwidth, latency, and capacity based on the user’s actual business requirements (including video, data, voice, etc.). It has always been the principle adhered to by Guoxin Longxin to tailor the most suitable solutions for users.
订阅评论
登录
0 Comments
最旧
最新
最多投票
内联反馈
查看所有评论